Private 5G adalah teknologi nirkabel yang menghadirkan konektivitas seluler ke jaringan pribadi, seperti bisnis swasta, penyedia pihak ketiga, dan pemerintah daerah.Dahulu, jaringan seluler terbatas pada operator nasional besar seperti T-Mo
Selengkapnya »»
AI is revolutionizing the world of cybersecurity, transforming how organizations detect and respond to threats. As AI continues to evolve, its ability to strengthen cybersecurity defenses grows, with experts anticipating even greater benefits as t
Selengkapnya »»
At RSA Conference 2024, Allan Liska of Recorded Future shared insights on evolving ransomware tactics and the significant law enforcement victory of exposing the leader behind the notorious LockBit ransomware group.The U.S. Department of Ju
Selengkapnya »»
At the RSA Conference 2024, Recorded Future unveiled alarming trends where nation-state actors increasingly disguise themselves as hacktivists to obscure genuine threats targeting organizations. These sophisticated masquerades fuel misinformation
Selengkapnya »»
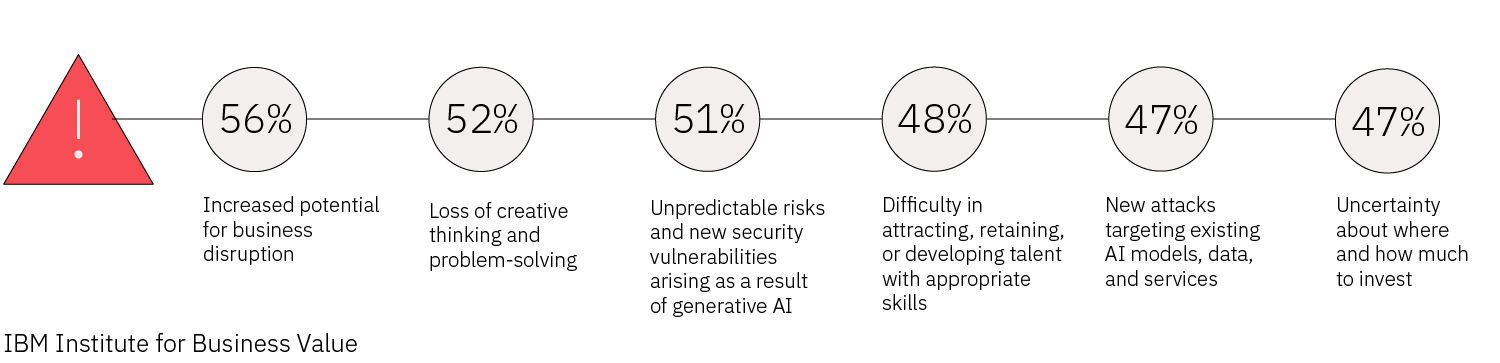
The rise of generative AI has been nothing short of meteoric, capturing global attention with its transformative potential. Yet, as this technology reshapes industries, it also brings with it a host of cybersecuri
Selengkapnya »»
In today’s rapidly evolving threat landscape, organizations must establish robust cybersecurity governance programs to ensure every employee understands their role in mitigating cyber risks. Yet, many businesses struggle to design and implement
Selengkapnya »»
A recent IBM survey reveals a worrying gap in AI security practices. While 82% of C-suite executives agree that trustworthy and secure AI is crucial for their organizations, only 24% have integrated security into their generative AI (GenAI) projec
Selengkapnya »»
To combat cybercrime effectively, companies must first understand how they are being targeted. Modern cybercriminals are no longer hobbyists or amateur hackers; they include state-sponsored groups and professional criminals aiming to steal informa
Selengkapnya »»
A recent CISA report has sparked debate about long-standing assumptions in the cybersecurity industry, challenging core beliefs about secure-by-design principles and DevSecOps methodologies. Delivered on October 1
Selengkapnya »»
Effectively combining threat intelligence and threat hunting offers organizations a comprehensive approach to cybersecurity. Here's how to integrate these two strategies to build a robust defense.Threat intelligence and threat hunting are d
Selengkapnya »»